Cybersecurity can be complex, but it’s all about protection. Here’s a simple analogy to help you visualize how your data is kept safe:
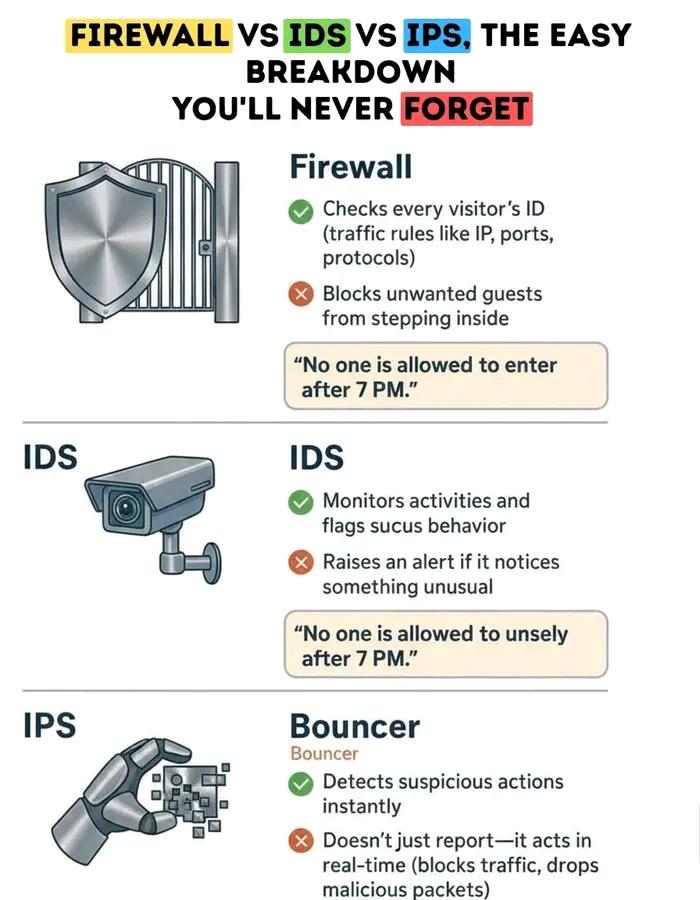
Firewall: The digital gatekeeper, blocking unauthorized access.
IDS: Like a surveillance camera, detecting suspicious activities.
IPS: A security guard preventing threats before they get in.
IP Address: Just like a vehicle’s license plate, it’s how we identify devices.
ACL: Access rules that determine who gets in, and who doesn’t.
SIEM: The central hub where security threats are detected and managed.
Just like a high-security checkpoint, every layer works together to defend against cyberattacks. Stay safe out there!
#CyberSecurity #Tech #DigitalSecurity #InfoSec
Firewall: The digital gatekeeper, blocking unauthorized access.
IDS: Like a surveillance camera, detecting suspicious activities.
IPS: A security guard preventing threats before they get in.
IP Address: Just like a vehicle’s license plate, it’s how we identify devices.
ACL: Access rules that determine who gets in, and who doesn’t.
SIEM: The central hub where security threats are detected and managed.
Just like a high-security checkpoint, every layer works together to defend against cyberattacks. Stay safe out there!
#CyberSecurity #Tech #DigitalSecurity #InfoSec
Cybersecurity can be complex, but it’s all about protection. Here’s a simple analogy to help you visualize how your data is kept safe:
🔐 Firewall: The digital gatekeeper, blocking unauthorized access.
🎥 IDS: Like a surveillance camera, detecting suspicious activities.
🛡️ IPS: A security guard preventing threats before they get in.
📍 IP Address: Just like a vehicle’s license plate, it’s how we identify devices.
📝 ACL: Access rules that determine who gets in, and who doesn’t.
🖥️ SIEM: The central hub where security threats are detected and managed.
Just like a high-security checkpoint, every layer works together to defend against cyberattacks. Stay safe out there! 💻
#CyberSecurity #Tech #DigitalSecurity #InfoSec
·226 Views
·0 Reviews