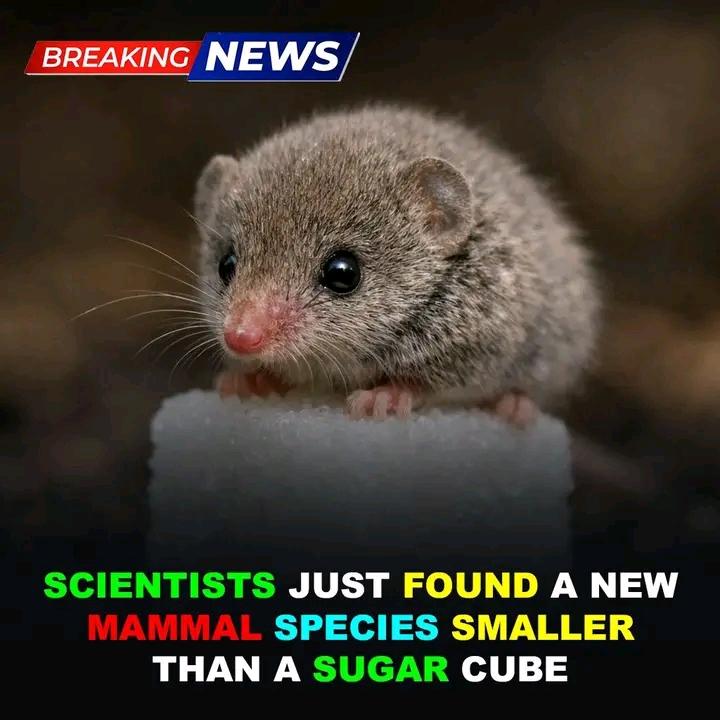
Scientists have confirmed the discovery of a newly recognized mammal, Crocidura stanleyi, a miniature dwarf shrew found in Ethiopia’s highland ecosystems. The species was formally identified through combined genetic sequencing and morphological examination conducted by researcher Evan W. Craig from the University of Massachusetts Boston. Initial field discovery occurred when Yonas Meheretu of the Swedish University of Agricultural Sciences encountered the animal during ecological surveys in southern Ethiopia.
The shrew’s scientific name honors William Stanley, whose earlier specimen collection in 2015 later became a critical reference point in distinguishing the animal as a previously undocumented species. The finding highlights the continuing importance of long-term field research, meticulous specimen preservation, and modern analytical techniques in uncovering biodiversity that remains hidden in remote habitats.
#fblifestyle #science #wildlife #discovery #nature
The shrew’s scientific name honors William Stanley, whose earlier specimen collection in 2015 later became a critical reference point in distinguishing the animal as a previously undocumented species. The finding highlights the continuing importance of long-term field research, meticulous specimen preservation, and modern analytical techniques in uncovering biodiversity that remains hidden in remote habitats.
#fblifestyle #science #wildlife #discovery #nature
Scientists have confirmed the discovery of a newly recognized mammal, Crocidura stanleyi, a miniature dwarf shrew found in Ethiopia’s highland ecosystems. The species was formally identified through combined genetic sequencing and morphological examination conducted by researcher Evan W. Craig from the University of Massachusetts Boston. Initial field discovery occurred when Yonas Meheretu of the Swedish University of Agricultural Sciences encountered the animal during ecological surveys in southern Ethiopia.
The shrew’s scientific name honors William Stanley, whose earlier specimen collection in 2015 later became a critical reference point in distinguishing the animal as a previously undocumented species. The finding highlights the continuing importance of long-term field research, meticulous specimen preservation, and modern analytical techniques in uncovering biodiversity that remains hidden in remote habitats.
#fblifestyle #science #wildlife #discovery #nature

·131 Views
·0 Reviews